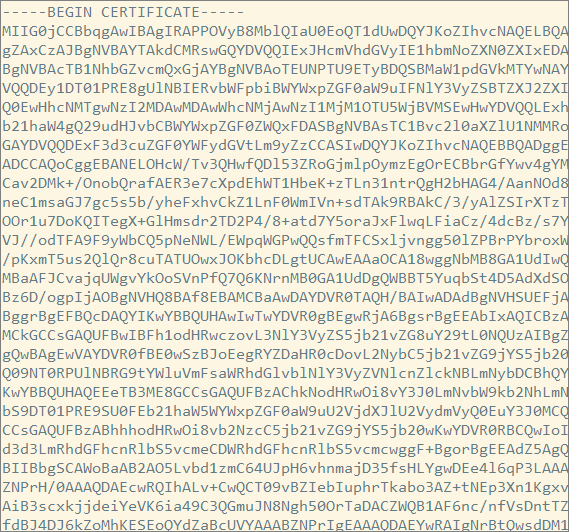
Transfer a PEM-based Certificate into a Java Keystore
This is something I don’t do often enough to remember, without looking it up each time.
We start with the following:
- A PEM-based SSL certificate file.
- A related private key file.
- A related chain of certificates to the root CA certificate.
For our purposes, we need to use this data in a Java application which expects a Java keystore file - for example, a Java-based web application, using Java’s SSL implementation (e.g. as opposed to using OpenSSL).
In some cases, the following optional step may be needed to prevent “error getting chain” problems:
|
|
Export the key, certificate and ca-certificate into a PKCS12 bundle:
|
|
When responding to the prompts, make a note of the password. Use the same password for the key as for the store.
For the “first and last name” prompt, make sure you use the domain name (e.g. my_web_site.com) - this is the CN. It must match the host name as it will appear in URLs for your web site.
Then create the JKS (the keystore file) using the Java keytool command:
|
|
Reference: Thanks to this article for guidance.
Additional notes from here:
In summary, there are four different ways to present certificates and their components:
PEM - Governed by RFCs, its used preferentially by open-source software. It can have a variety of extensions (.pem, .key, .cer, .cert, .crt, more)
PKCS7 - An open standard used by Java and supported by Windows. Does not contain private key material.
PKCS12 - A Microsoft private standard that was later defined in an RFC that provides enhanced security versus the plain-text PEM format. This can contain private key material. Its used preferentially by Windows systems, and can be freely converted to PEM format through use of openssl.
DER - The parent format of PEM. It’s useful to think of it as a binary version of the base64-encoded PEM file. Not routinely used very much outside of Windows.